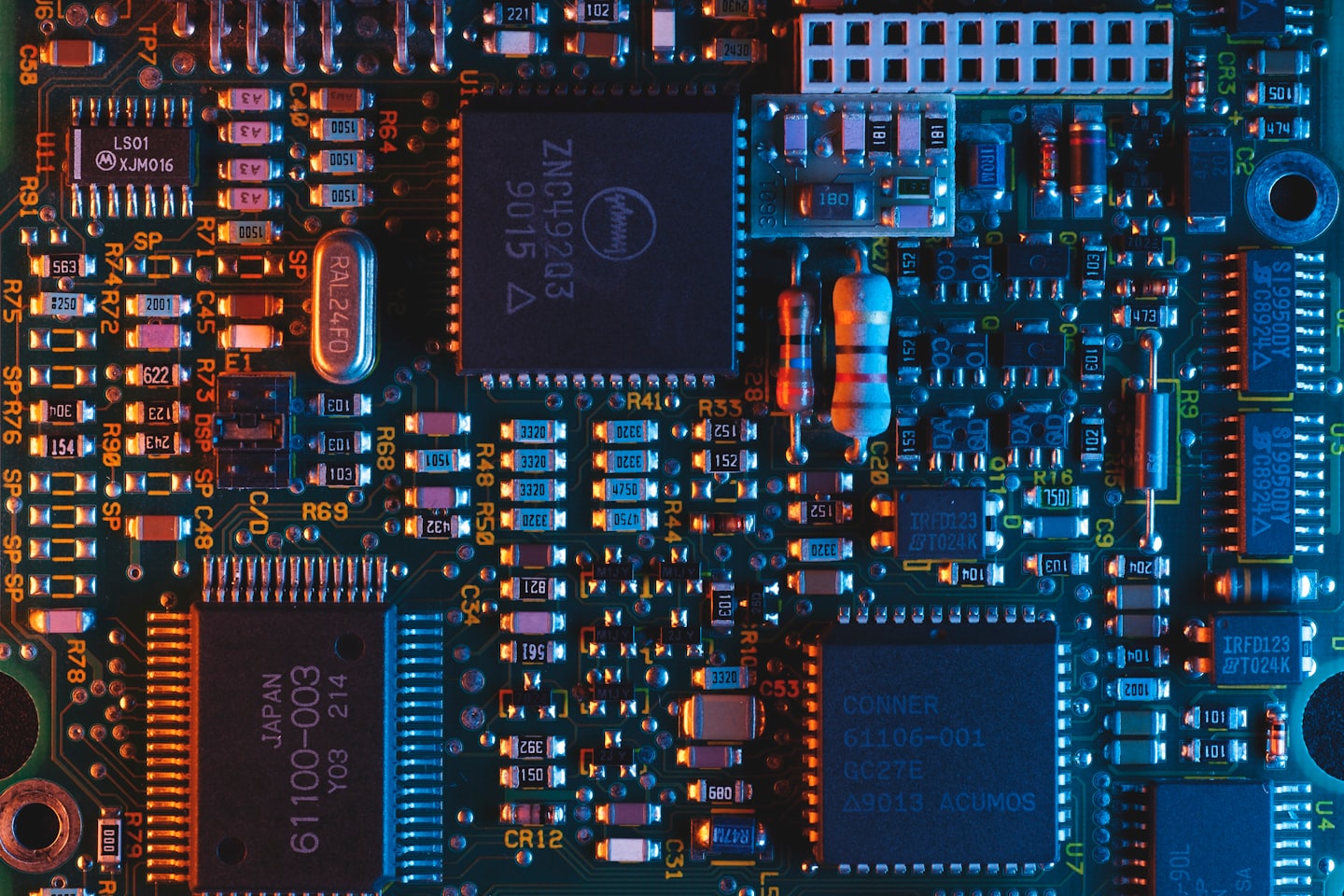
Stay Informed on Emerging Cybersecurity Threats
Discover curated resources to deepen your expertise in information security.
Network Security Basics
Master fundamental principles to protect digital communications.
Advanced Penetration Testing
Unlock cutting-edge tactics to identify and exploit vulnerabilities.
Cryptography Essentials
Gain critical insights into encryption methods and data protection.
Explore the Latest in Cybersecurity Trends
Find clear, concise answers to your most pressing cybersecurity questions here.
What are the essential skills to start a career in information security?
Fundamental skills include networking, system administration, and understanding of security principles.
How can I stay informed about emerging cyber threats?
Subscribe to trusted cybersecurity news feeds and follow expert blogs like Jordan Hacks.
What tools are recommended for penetration testing beginners?
Popular tools include Nmap, Metasploit, Wireshark, and Burp Suite.
How often should I update my security software?
Regular updates are crucial; ideally, enable automatic updates for continuous protection.
What is the importance of ethical hacking in cybersecurity?
Ethical hacking helps identify vulnerabilities before malicious hackers can exploit them.
Can I build a cybersecurity portfolio with personal projects?
Absolutely! Document your labs, analyses, and any security research to showcase your skills.
Inspiring Journeys from InfoSec Enthusiasts
This resource guides you through essential cybersecurity concepts, enabling you to enhance your skills confidently.
How a Cybersecurity Expert Built a Strong Portfolio
This case study details how a professional tackled security challenges using advanced techniques, boosting protection and expertise.


Sustaining Growth with Innovative Security Practices
This case study examines how a specialist refined methods, enhanced defenses, and delivered significant security improvements.
Enhancing Cyber Defenses with Targeted Approaches
This case study highlights how leveraging key tools improved threat detection, reduced vulnerabilities, and increased efficiency.